Analyzing the $4M Makina Finance Exploit
Overview
On January 20, 2026, Makina Finance fell victim to a sophisticated oracle manipulation attack, resulting in a loss of approximately $4.13 million. The attacker exploited the protocol’s reliance on spot pricing from a Curve Finance pool to manipulate the value of the MachineShareOracle. By heavily distorting the liquidity in the underlying DUSD/USDC pool via a flash loan, the attacker was able to artificially inflate the share price, deposit assets at this manipulated value, and subsequently exit with a significant profit.
Attack Transaction: 0x569733b8016ef9418f0b6bde8c14224d9e759e79301499908ecbcd956a0651f5
Attacker Address: 0x935bfb495E33f74d2E9735DF1DA66acE442ede48
Deep Dive
Attack Flow
The exploitation followed a classic “pump-and-dump” pattern using flash loan liquidity to skew on-chain price feeds.
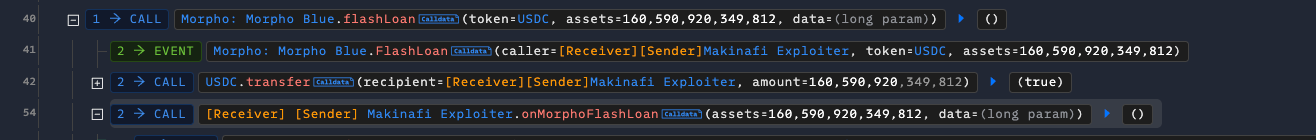
Flash Loan: The attacker borrowed a massive amount of liquidity (approximately 280 million USDC) to secure the capital needed for manipulation.
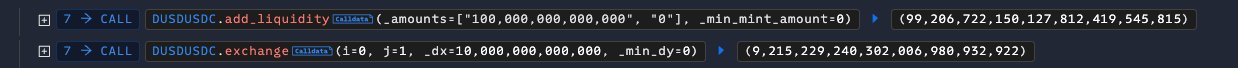
Market Distortion: The attacker deployed roughly 170 million USDC into the DUSD/USDC Curve pool. This unbalanced the pool significantly, distorting the output of
calc_withdraw_one_coinand the spot price reported by the pool.Oracle Update: Makina’s
MachineShareOracleupdated its internal price based on this manipulated state. Because the protocol relied on the spot liquidity/balance of the Curve pool without sufficient Time-Weighted Average Price (TWAP) or liquidity cap checks, thesharePricewas artificially inflated.Arbitrage Execution:
With the
sharePriceinflated, the attacker interacted with the Makina Machine, depositing/swapping the remaining 110 million USDC against the protocol’s liquidity.Due to the distorted valuation, the protocol credited the attacker with significantly more shares/value than the true market rate.
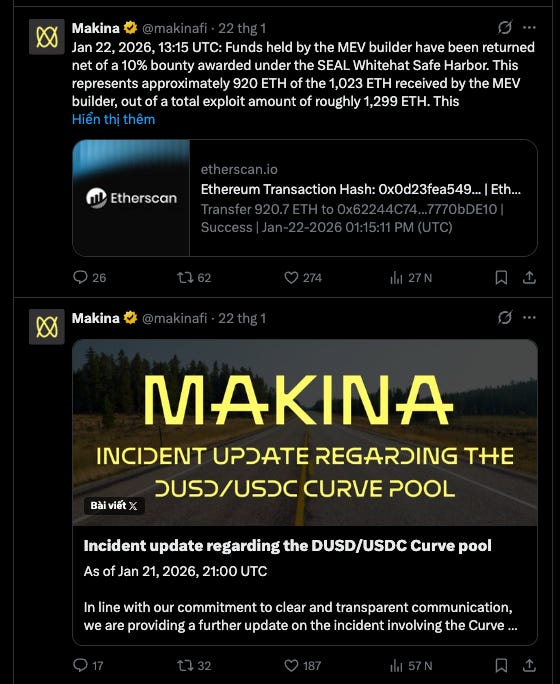
Exit & Profit: The attacker reversed the pool manipulation (or simply withdrew) and paid back the flash loan, pocketing the difference—roughly $4.13M (mostly captured by an MEV builder).
Root Cause
The core vulnerability was the protocol’s dependency on a spot price oracle derived from a manipulatable liquidity pool (Curve). In DeFi, relying on the instantaneous balance or get_dy/calc_withdraw_one_coin of an AMM pool is inherently risky if the pool’s liquidity is low relative to the potential flash loan size. The MachineShareOracle failed to filter out the extreme volatility introduced by the flash loan.
Recommendations
Implement TWAP Oracles: Replace spot price feeds with Time-Weighted Average Price (TWAP) oracles (e.g., Chainlink, Uniswap V3 TWAP) to smooth out price spikes within a single block.
Flash Loan Protection: Disallow critical share price updates or deposits/withdrawals in the same transaction as massive liquidity shifts (though this can be bypassed with multi-block attacks, it raises the cost).
Liquidity & Slippage Checks: Implement strict deviation checks. If the on-chain price deviates significantly from an external benchmark (or a secondary oracle), the transaction should revert.
Conclusion
The Makina Finance incident serves as a stark reminder that oracle design is the bedrock of DeFi security. Even with complex logic, the external dependency on AMM states requires rigorous threat modeling against flash loans.
However, internal testing is rarely enough. To avoid becoming another statistic in a post-mortem thread, protocols must prioritize rigorous audits from top-tier firms that specialize in complex attack vectors.