Deep Dive into the dTRINITY cbBTC Exploit
On March 17, 2026, the DeFi protocol dTRINITY, a lending protocol on Ethereum, suffered a security incident resulting in an estimated loss of ~$257.3K.
Overview
On March 17, 2026, the DeFi protocol dTRINITY, a lending protocol on Ethereum, suffered a security incident resulting in an estimated loss of ~$257.3K.
The exploit stemmed from an empty market weakness commonly found in forks of Aave V3, where reserves with extremely low liquidity can behave unpredictably. In this scenario, repeated accumulation of flash loan premiums caused the liquidityIndex to increase to an abnormally high level, disrupting the accuracy of the reserve’s accounting. This distortion led to precision issues in deposit and withdrawal calculations, enabling the attacker to artificially inflate collateral value, borrow dUSD against it, and reclaim the deposited cbBTC for a net gain.
Technical Analysis of the Exploit
Incident Overview
Date: March 17, 2026
Protocol: dTRINITY
L2Pool Contract: 0xfda3a0effe2f3917aa60e0741c6788619ae19e84
Exploiter Address: 0x08cfdff8ded5f1326628077f38d4f90df6417fd9
Attack Transactions:
Root Cause
The exploit stemmed from an empty market vulnerability in the lending pool of dTRITINY, an AAVE V3–style implementation, where the cbBTC reserve operated with near-zero liquidity.
At the core of the issue is the protocol’s liquidity index update mechanism, which is triggered on every flash loan repayment through _handleFlashLoanRepayment and is defined as:
Under these conditions, repeated flash loan premium accrual caused the reserve’s liquidityIndex to increase disproportionately, as the index update mechanism scales inversely with total liquidity. With minimal liquidity, even small premiums led to significant index inflation.
This created a misalignment between scaled balances and underlying assets, introducing a rounding asymmetry in which:
Small deposits minted shares at an artificially low cost
Withdrawals redeemed disproportionately higher value
As a result, the attacker was able to inflate collateral value, borrow against it, and extract real assets from the protocol.
Attack Flow
The exploit was executed across two sequential transactions, leveraging abnormal growth of the liquidityIndex in a near-empty cbBTC reserve.
liquidityIndex Manipulation Transaction
Transaction: 0x8d33d688def03551cb77b0463f55ae5a670f5ebf3bbb5b8aa0e284c040ae7139
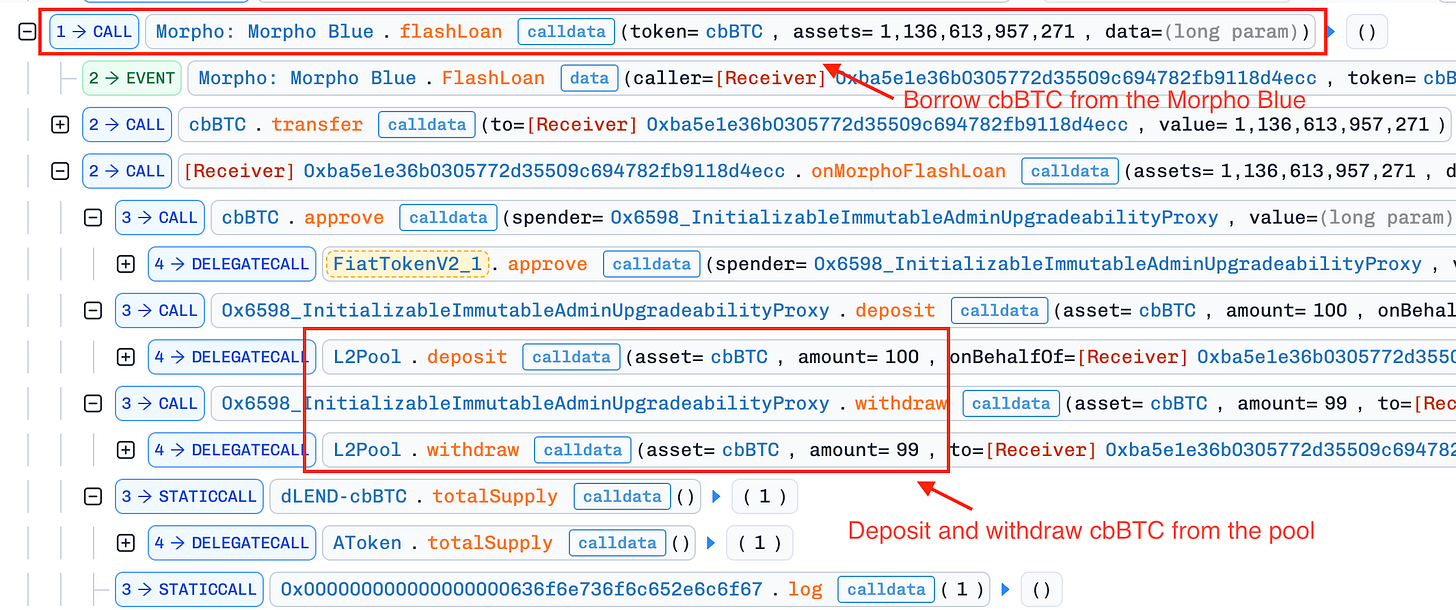
The attacker executed a multi-step strategy to manipulate the internal accounting of the cbBTC reserve, ultimately inflating the liquidityIndex far beyond its true economic value.
Borrowed
cbBTCfrom Morpho Blue and deposited it into thedLEND-cbBTCpool, minting 100 scaled shares.Withdrew 99 shares, leaving only a share balance and effectively reducing the reserve to an almost-empty state.
Transferred 0.8 cbBTC directly to the dLEND-cbBTC aToken contract.
Repeatedly invoked
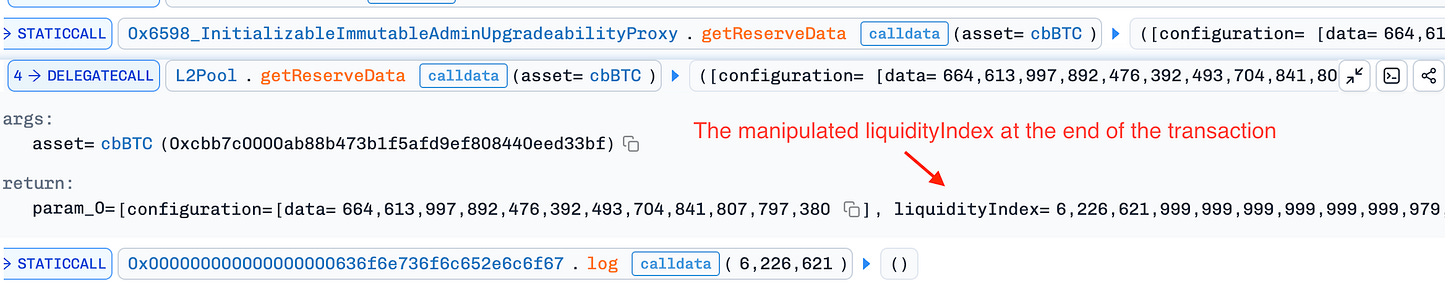
flashLoanoperations to accumulate premiums into the reserve, causing theliquidityIndexto increase disproportionately (reaching ~6.22e27)Performed additional deposit/withdraw cycles to extract residual liquidity from the pool
Repaid the flash loan
At the end of this transaction, the reserve was left in a distorted state, where the liquidityIndex was significantly inflated relative to actual liquidity.
Collateral Inflation and Profit Extraction Transaction
Transaction: 0xbec4c8ae19c44990984fd41dc7dd1c9a22894adccf31ca6b61b5aa084fc33260
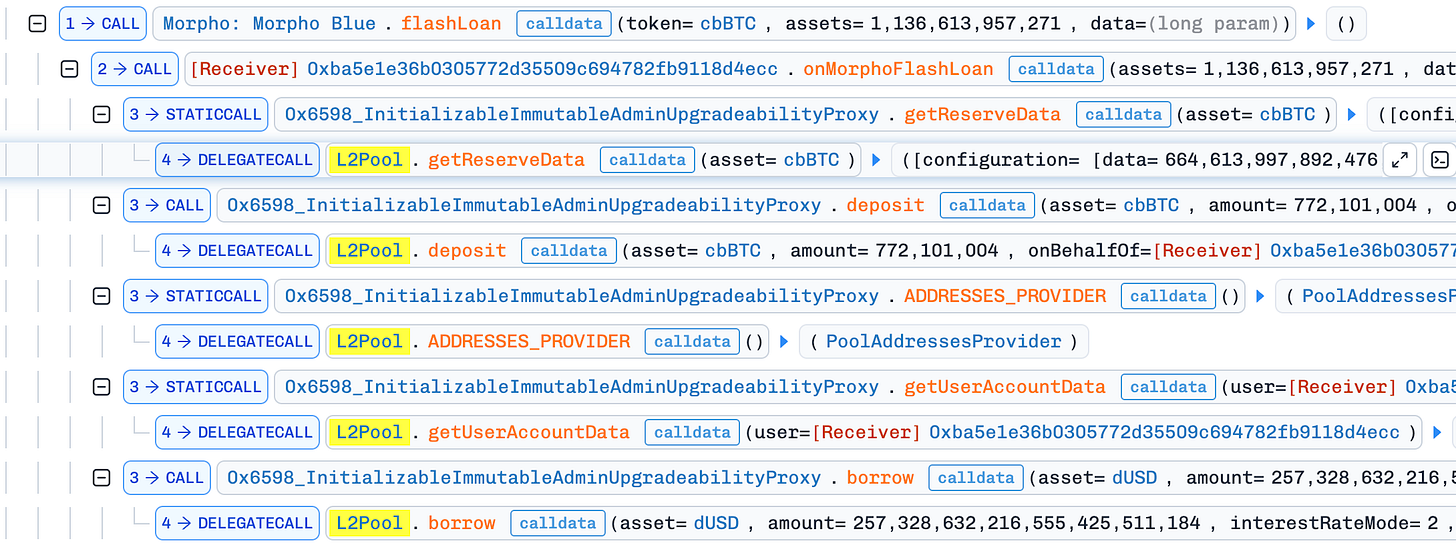
With the manipulated reserve state in place, the attacker proceeded to extract value by leveraging the inflated liquidityIndex.
Borrowed cbBTC again from Morpho Blue and deposited ~7.72 cbBTC into the compromised reserve. Due to the inflated
liquidityIndex, the deposit was overvalued, resulting in an artificially large collateral position.Used this inflated collateral to borrow approximately ~257.3K dUSD from the dLEND-dUSD market.
Continued extracting cbBTC through repeated deposit and withdrawal cycles.
Repaid the flash loan and transferred the borrowed dUSD to the attacker’s externally owned account (EOA)
Conclusion
This incident highlights how flaws in index-based accounting under low-liquidity conditions can be exploited to create severe economic distortions. By reducing the cbBTC reserve to a near-empty state and artificially inflating the liquidityIndex through flash loan premiums, the attacker was able to overvalue collateral and borrow assets far beyond legitimate limits. The exploit underscores the importance of enforcing liquidity constraints and ensuring that critical accounting variables remain tightly aligned with actual underlying value.