LAXO Token Exploit: AMM Reserve Manipulation via Burn Mechanism
On February 22, 2026, the LAXO token on Binance Smart Chain (BSC) was exploited through a flaw in its token transfer logic and burn mechanism. The vulnerability allowed an attacker to manipulate the reserve accounting of the LAXO/USDT PancakeSwap liquidity pool.
Incident Overview
Date: Feb 22, 2026
Platform: Binance Smart Chain (BSC)
Attacker Address: 0x17f9132E66A78b93195b4B186702Ad18Fdcd6E3D
Attack Contract: 0x6588ACB7dd37887C707C08AC710A82c9F9A7C1E9
Laxo Token Contract: 0x62951CaD7659393BF07fbe790cF898A3B6d317CB
Attack Transaction: 0xd58f3ef6414b59f95f55dae1acb3d5d6e626acf5333917c6d43fe422d98ac7d3
Exploit Mechanics
All steps below were executed within a single transaction by the attack contract:
Borrowed 350k USDT from a PancakeSwap V3 pool using a flash loan.
Bought a large amount of LAXO tokens from the LAXO/USDT pool, temporarily stored them in PancakeRouter.
Added a small amount of liquidity (BNB and LAXO) and immediately removed it.
This trick allowed the attacker to retrieve the temporarily stored tokens from PancakeRouter and avoid the swap fee from step 2.
Sold all LAXO tokens back into the LAXO/USDT pool.
This action triggered the burn mechanism, which incorrectly updated the reserves in the PancakeSwap pool. The attacker was then able to withdraw 487k USDT.
Repaid 350,175 USDT to the PancakeSwap V3 pool to settle the flash loan.
Root Cause Analysis
The root issue occurs in step 4, where the PancakeSwap pool updates its reserves incorrectly.
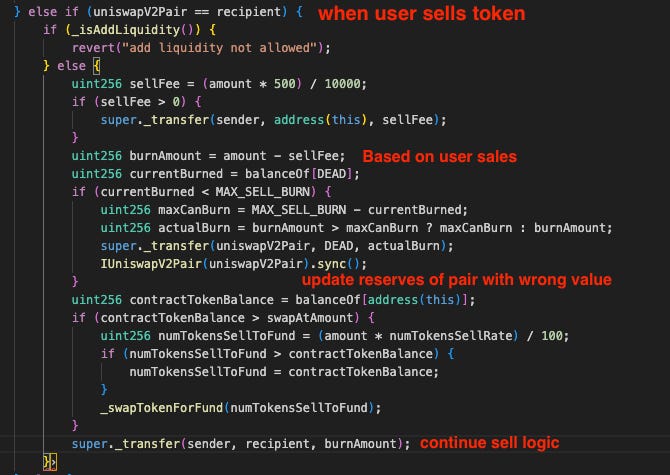
A deeper look into the _transfer internal function of the LAXO token reveals a burn mechanism triggered when users sell tokens. The problem lies in the position of the sync call.
The contract executes sync after transferring tokens from the pair to the dead address (burn). The sync function updates the pair reserves based on the remaining LAXO and USDT balances in the pair contract.
The sync action occurs immediately after burning, causing the pair to record incorrect reserves. This inflates the LAXO reserve value, enabling the attacker to extract excess USDT from the pool when selling the remaining LAXO tokens.
Conclusion
The LAXO exploit highlights the risks of improper token logic interacting with AMM liquidity pools. A misordered burn operation and sync call caused the PancakeSwap pair to record incorrect reserves. This broke the pool’s reserve accounting and allowed the attacker to extract excess USDT. The incident shows that token mechanisms such as burns or fees must be carefully designed to avoid interfering with pool reserve updates. Projects should thoroughly review and test how their token contracts interact with AMM pools to ensure reserve calculations remain accurate and secure.